Mitar's Point
science, technology, nature and (open) society.
Contact
Slovenian TDM exceptions and content available online
Does lawful access under the Slovenian TDM exceptions also include content that is freely available online?
To answer that question, I submitted a complaint to the European Commission in June 2024 alleging that the Republic of Slovenia had not properly implement the Directive (EU) 2019/790 on copyright and related rights in the Digital Single Market (hereinafter: the CDSM Directive). The complaint argued that Articles 57.a and 57.b of the Slovenian Copyright and Related Rights Act (hereinafter: ZASP), which regulate the exceptions for text and data mining (hereinafter: TDM exceptions), fail to explicitly provide that the notion of “lawful access” includes content that is freely available online. The European Commission did not initiate infringement proceedings against Slovenia, reasoning that although the Slovenian implementation does not explicitly mention freely available online content as part of the notion of lawful access, it also does not expressly exclude it. Consequently, it may be interpreted that freely available online content forms part of lawful access under the TDM exceptions in ZASP.
dinit
I made an opinionated init specially for Docker containers: dinit. It supports running and managing multiple programs, their stdout and stderr, and handling signals, all in the way more suitable for Docker containers. Using it means no more resource exhaustion from zombie processes, data loss by uncleanly terminated containers, stray daemonized processes that keep running, or hidden issues because failed processes inside a container gets restarted instead of taking the whole container with them.
regex2json
I made a simple tool regex2json in Go to convert traditional text-based (and line-based) logs to JSON for programs which do not support JSON logs themselves. But the tool is more general and can enable any workflow where you prefer operating on JSON instead of text. It works especially great when combined with jq. I was inspired by this blog post.
Nonenumerable database
Sometimes it is useful to first define an abstraction. A good abstraction can reveal that some problems could be solved by the same solution. A good abstraction also makes it easier for us to communicate about the solution and understand its properties.
One such abstraction which I think should be defined and named is nonenumerable database. A database where you can query a value by a key, but you cannot enumerate all keys (nor all values). Even a database operator/administrator is not be able to do so.
At the same time, some problems are more intuitive than others and can help us better understand or even inform the abstraction. We will look at three examples where nonenumerable database can help: DNS/DNSSEC, gun ownership registry, and voting.
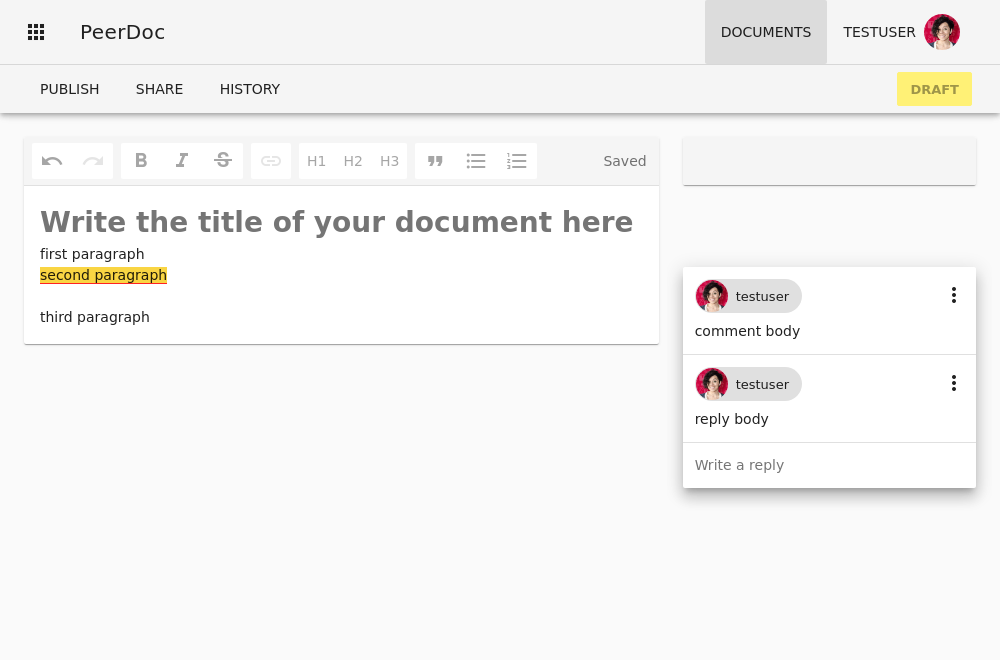
PeerDoc – Scaling real-time text editing
PeerDoc is a collaborative real-time rich-text editor with undo/redo, cursor tracking, inline comments, permissions/sharing control over documents, a change history. Things you would expect from a modern collaborative editor on the web.
But the main difference is that it combines two types of collaboration:
- real-time collaboration between collaborators on the draft of the document (push-based collaboration)
- fork and merge request style of collaboration with others, allowing collaboration to scale beyond a small group of collaborators (pull-based collaboration)
JSON decoding in node is fast
I made a benchmark comparing how long it takes to decode JSON in node.js and Go. As I have noticed in the past, JSON decoding in node.js is really fast.
Google search across languages
In 2013, I wrote how crowdsourcing could help break out of the language bubble we all find ourselves in when we search online. How our search results only come from the language we write our search keywords in. But since then, machine translation between languages has greatly improved. So why are we still in our language bubbles?
There are some rays of hope. Google is reportedly able to return you results from other languages when there are no good hits in your primary language. I have to say, though, that I have never experienced this. Maybe because I usually search in English. I would guess that when you search in smaller languages, you sometimes get English results added.
But I want the opposite. I want to see ideas and thoughts and solutions that might be available in other languages, the languages I do not speak, when I search in English. I want diversity. I think all the pieces to build this are available. Why is this not already available? Am I overlooking any obstacle to this?
Store IDs in MongoDB as binary or as string?
I was curious if MongoDB compression can efficiently store IDs if they are represented as string instead in a more compact binary form. So I made a benchmark and measure compression performance of three available compressors: zlib, snappy, and zstd.
Can humans grow up in zero gravity?
Gravity seems to be our first and most important teacher. Patient, consistent and always present. Children can learn cause and effect through it. What happens if I lift an object and let go? Over and over again. On repeat. Always the same thing.
When we think about life in space. Can we raise children there? Can children grow up in zero gravity? Can they develop their mental abilities without having this teacher around them? Or will they develop in other ways? A different kind of logic?
Database-abstraction APIs should not exist
Database-abstraction APIs where you write a query using the host programming language should not exist. Or more precisely, should not have to exist. For example, in Django you can query the database using the following Python code:
Entry.objects.filter(is_draft=True)
Which Django translates (roughly) into the following SQL:
SELECT *
FROM blog_entry
WHERE is_draft = true;
But why we cannot write SQL query directly as an SQL query, while retaining all other features Django offers through its database-abstraction API (database agnostic code, inputs to queries and outputs from queries being Python objects, etc.)? I claim there is no reason anymore for that.